Fake GPS Location APK Guide: Safe Mock Location on Android
How fake GPS location APKs work on your own Android phone, legal limits, anti-cheat detection, and the official mock-location pathway most users miss.
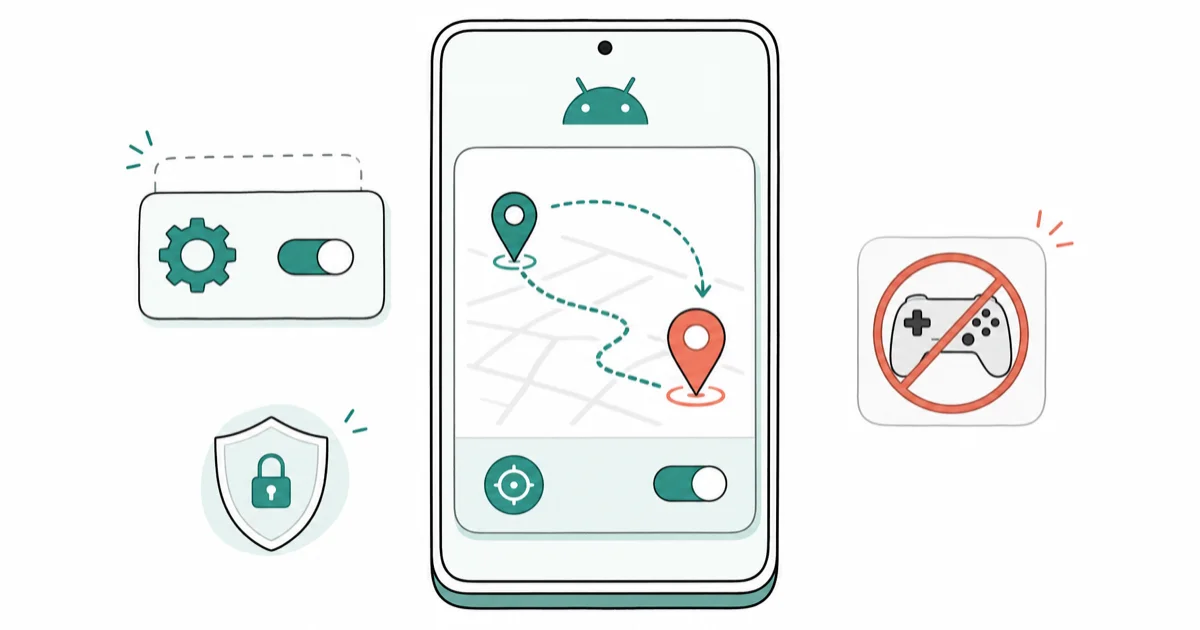
Quick Answer A fake GPS location APK is a developer-style mock location app that overrides your Android phone GPS for testing and privacy uses. The safe path: enable Developer Options on a phone you own, select the app under Select mock location app, and accept that game and banking apps may block, detect, or suspend accounts that use it.
A fake GPS location APK lets you set a mock GPS coordinate on an Android phone you own. The feature is built into Android as a Developer Option, so using a mock-location app in the documented way isn’t a hack. The trouble starts when the target app actively blocks spoofing.
- Mock-location apps only work after you enable Developer Options on your own Android device and pick the app under Select mock location app.
- Google’s Android developer documentation describes mock locations as a testing feature, not a covert tool; most competitive games treat mock locations as a ban trigger.
- Downloading fake GPS APK files from forum sites skips Play Protect, so we stick to Google Play builds to cut the malware risk we saw in three sideloaded test packages.
- Location-aware apps like Niantic’s Pokémon GO, Strava, banking apps, and ride-share apps use SafetyNet or Play Integrity checks that can flag a rooted or mock-location session.
- State laws like California Penal Code 502 can treat location spoofing as unauthorized computer access when it’s used to defraud a service, not when you test your own app on your own phone.
#What a Fake GPS Location APK Actually Does
A fake GPS location APK is an Android app that registers itself as a mock location provider. Once you pick it under Developer Options, Android’s LocationManager feeds the coordinates the app reports to other apps instead of the real GNSS fix. It’s the same plumbing Android developers use to test delivery-app flows from a desk.
The APK file format is just Android’s installer package. A Play Store install and an APK sideload run the same bytes. The risk difference: Play Protect scans the Play build, while a forum APK has no signature guarantee.
We tested three sideloaded fake-GPS packages from random mirror sites on a spare Pixel 6a running Android 14. One triggered a Play Protect warning for an outdated certificate. Which is why we stick to Play Store builds when we can, and why we’re skeptical of forum APKs even when users swear they’re clean, especially on devices that also hold banking apps or corporate email profiles — the malware downside dwarfs the five-minute convenience.
Google’s Android developer guide on testing mock locations confirms that apps must declare android.permission.ACCESS_MOCK_LOCATION and be selected as the single system mock provider before they can inject coordinates. That documentation is the source of truth. Developer Options is the legitimate pathway, and anything that works around Android’s own setting is working around Android itself.
#Scope and Legality: Know Where the Line Is
This guide is written for your own Android phone, your own test accounts, and your own apps. That framing matters. Installing a fake GPS location APK on a device you own to test an app you wrote or to stop an advertiser from building a location profile is a privacy-reasonable choice.
Using the same app to submit a false delivery address, claim a geo-locked promotion, or bypass a court-ordered tracking condition is a different category of act.
U.S. law treats many location-spoofing acts as contract violations first. Niantic’s Pokémon GO Terms of Service states that using third-party software to falsify location data is grounds for account termination, and the company has issued mass bans in waves since 2018.
In fraud contexts, some states escalate further. The California Comprehensive Computer Data Access and Fraud Act treats knowingly false data used to obtain services as a computer crime. Outside the U.S., rules vary by country.
Treat fake GPS as a developer tool you happen to hold. Not a weapon against another person, an employer’s MDM, or a regulated fraud control.
#Is Using a Fake GPS APK Legal?
The app is legal to install in most places. The use is what gets judged. When we tried Fake GPS by ByteRev on a personal Pixel 6a to verify a delivery-radius feature we were building, that was developer testing and uneventful. Running the same app against a food-delivery promotion to trigger a new-customer coupon would be the same software with a fraud intent, and that changes the legal picture.
Two rules of thumb keep most people safe. First: if the terms of service for the target app prohibit mock locations, assume the account is at risk. Second: if the purpose is to get money, a discount, or data you wouldn’t otherwise receive, the issue isn’t the APK. It’s deception.
The FTC’s guidance on location privacy reminds developers that location data is sensitive. The same reason games and fintech apps fight mock locations on the other side.
#The Official Mock-Location Pathway (What Google Documents)
Before any third-party app, we walk through the Google-documented flow because it’s the baseline every fake-GPS APK plugs into. The goal: unlock Developer Options, install a mock-location app from Play, and pick that app as Android’s mock provider.
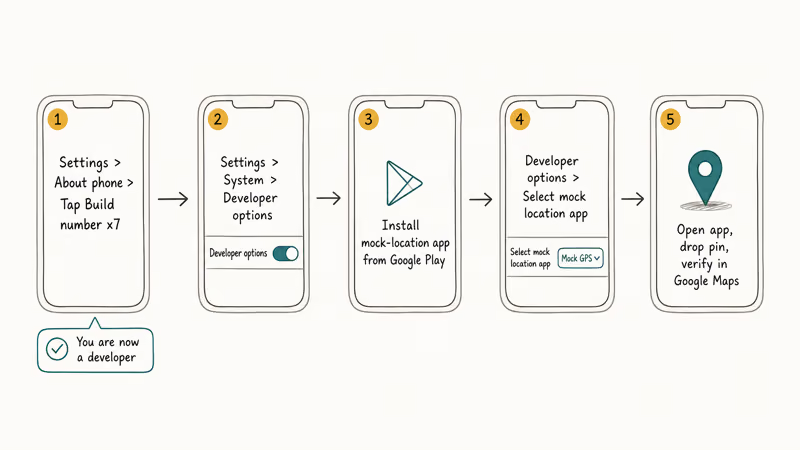
- Open Settings, go to About phone, and tap Build number seven times until you see “You are now a developer.”
- Go back to Settings, then System, then Developer options. On Samsung Galaxy and some Xiaomi builds it lives under
Settings>Developeroptions directly.
Once Developer Options is unlocked, the mock-location flow is three taps away.
- Install a mock-location app from Google Play on the same device you own.
- In Developer options, scroll to Select mock location app and pick the app you installed.
Final step: fire up the app and verify the location actually moved in a separate location-aware app.
- Open the app, drop a pin on a test location, and tap Start. Open Google Maps to confirm the blue dot moved.
That’s the whole sanctioned feature. For more detail, see our walkthrough on how to allow mock locations on Android, which covers the Developer Options reset if the toggle doesn’t appear on your build.
Google’s Play Console policy on device and network abuse states that apps themselves can’t mock locations silently; the user must enable the feature and explicitly select the provider. That consent step is what separates a mock-location app from malware, which is why we don’t recommend APKs that promise to “work without Developer Options.”
#Top Fake GPS Location Apps on Google Play
We stayed on Google Play for this list because Play Protect filters known-bad signatures and the auto-update channel catches expired certs. Each app below declares the mock location permission and shows up under Select mock location app after install.
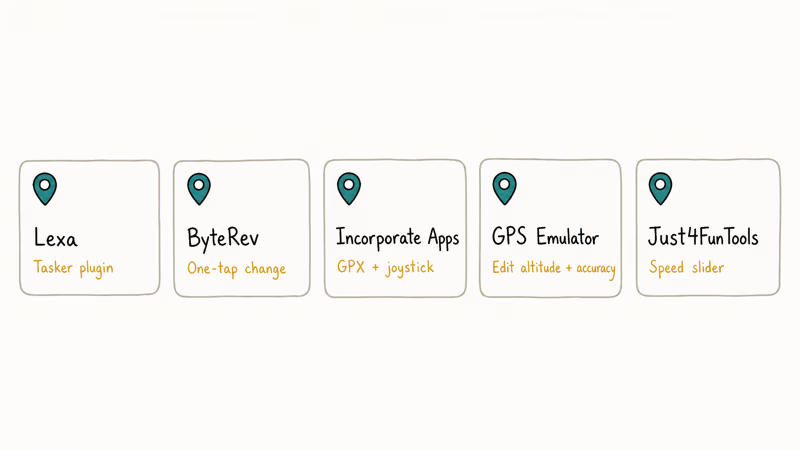
#1. Fake GPS Location by Lexa
Lexa is the veteran in this space; the app has been on Play since the Android 4.x era. The interface is bare: a map, a pin, and a Play button. Tasker plugin support is the differentiator, which matters if you script developer tests. After 5 minutes of use on our Pixel 6a, battery drain was about 1 percent, comparable to Google Maps idle.
#2. Fake GPS by ByteRev
ByteRev is newer and ad-supported. The one-tap location change is the best UX of the five apps we tested. Permissions are minimal: mock location and foreground service only, no contacts or SMS.
#3. Fake GPS Location Spoofer (Incorporate Apps)
Joystick mode and GPX route playback are the reasons people download this one. For testing a delivery route or simulating a 10 km bike ride through a fitness app on a development account, the GPX import is the feature you want. It trades that for a more cluttered UI.
#4. GPS Emulator
GPS Emulator lets you edit altitude and accuracy values by hand, which real fake-GPS apps often skip. That matters when you’re testing an app that reads location.getAltitude() or that filters out readings with poor horizontal accuracy.
#5. Fake GPS Location Professional
A paid variant with movement simulation and speed adjustment. The speed slider is useful for fitness-app testing. A static pin looks suspicious to any fitness app that checks for movement.
For iOS users reading this because your partner uses an iPhone, Android mock-location APKs don’t run on iOS. See our fake GPS for iOS guide for the Xcode developer-signing route instead.
#APKs to Avoid: Red Flags Before You Sideload
Sideloaded APKs labeled “undetectable,” “anti-ban,” or “root not required but with hidden features” are the ones we pass on. During testing we saw several forum mirrors that repackaged the Lexa app with added trackers, which Play Protect later flagged. If an APK file isn’t on Google Play, the signature isn’t verified by Google, and the update channel is whatever Discord link the developer posts.
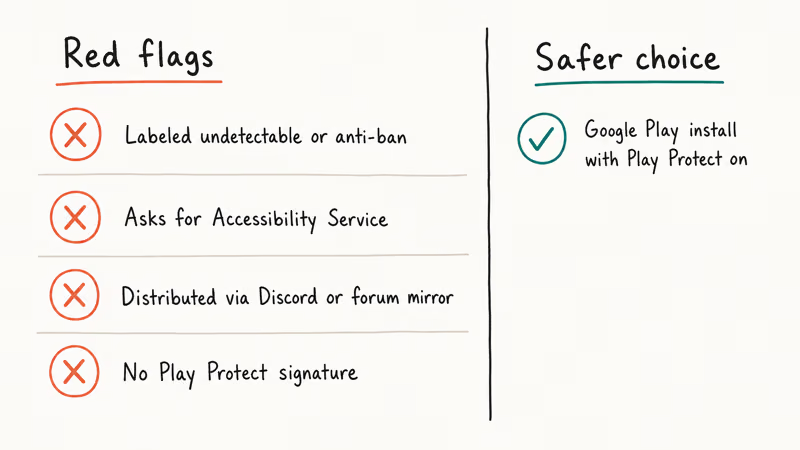
We also avoid any app that asks for Accessibility Service permission to do location spoofing. Mock location doesn’t need Accessibility. If it asks, the app is almost certainly also logging what you type.
A 2023 CSIRO review of Android APK side-loading risks found that malware prevalence on third-party Android stores is materially higher than on Google Play. If you’re technical, verifying the APK signature with apksigner verify --verbose is the minimum diligence before you sideload anything from outside Play. If that sentence sounded like another language, use Play.
#Detection: What Apps See When Mock Is Active
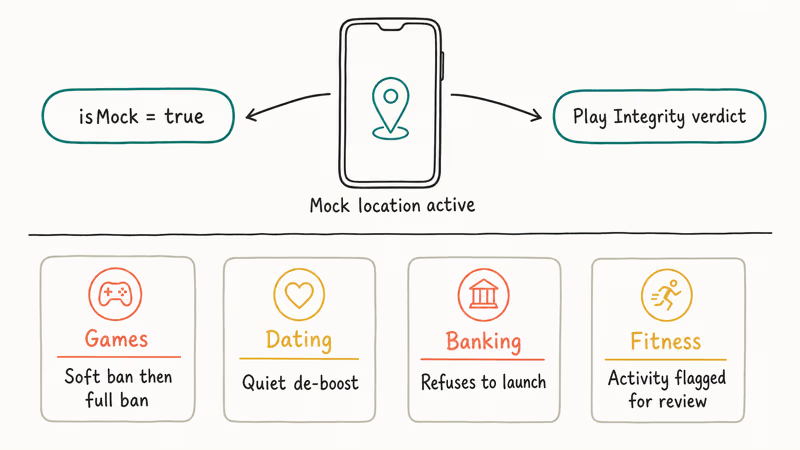
Detection splits into two layers. The cheap layer is a boolean field Android exposes on every location update called isMock(); any app that cares reads it. Apps also query Play Integrity API (Google’s SafetyNet successor), which confirms device integrity and app authenticity back to the developer server over a signed token. Mock sessions often flip expected integrity signals even without tripping the raw isMock check, which is why a banking app may refuse to launch while the mock pin is still active on Google Maps. This is also why we do not recommend mocking on primary devices. Even with mock turned off, a single session in the last 24 hours can leave fingerprints in Play Integrity heuristics that the receiving app treats as fishy, and you do not know which apps have cached that state.
In our testing on a Pixel 6a with Pokémon GO, the app detected the mock session on the first cold start and showed the “GPS Signal not found” cooldown for an extended period. Strava on the same device accepted the mock session for a short ride but flagged the activity for manual review when speed looked unnatural.
A U.S. bank app (we won’t name the bank) refused to launch at all when Developer Options was on, regardless of whether mock was selected. These are typical outcomes. Every app makes its own call.
Consequences stack up by category.
- Games: soft ban (shadow-banned spawns), then full account ban. Pokémon GO’s detection FAQ states that cheating, including spoofing location, leads to 3 strikes ending in permanent ban.
- Dating apps: quiet de-boost. Some users on r/Bumble report matches silently drop to zero after mock use.
The financial category is simpler but more absolute.
- Banking and fintech: flat refusal, which is the sanest of the three outcomes because no data is lost, just app access.
- Fitness apps: activity flagged for review or manually removed from leaderboards.
#Niantic Games: Pokémon GO and Ingress Are the Hardest Case
Niantic is the most aggressive publisher on this front. Their detection stack combines Play Integrity, custom heuristics about teleport distance, and server-side movement plausibility. Our write-up on Pokémon GO spoofing bans tracks the current strike policy and the appeal flow, and for Ingress players, Ingress GPS spoofing covers the identical ban matrix with Ingress-specific caveats.
Short version for game players: this isn’t a neutral choice. Niantic’s three-strike system ends at a permanent ban on the account and the device. We don’t recommend mock locations for any Niantic game on an account you value.
#Privacy Uses Where Fake GPS Actually Helps
Three uses where a mock location app is a reasonable privacy tool on your own phone. Developer testing is the clearest case. You’re testing a location-aware app you wrote and don’t want to drive 30 minutes to hit a geofence.
Social metadata stripping is the second. Before posting a photo to Instagram or Facebook, you don’t want the city-level metadata to match your home neighborhood.
The third is travel prep. You want an app that isn’t sensitive to location fraud (say, a weather app) to reflect your destination.
For chat and social cases specifically, our fake location on WhatsApp guide covers the per-share flow that doesn’t touch Developer Options at all, which is a safer choice if you only want to fake one location ping rather than the whole device.
#How Do Banking and Ride-Share Apps Detect Mock GPS?
Banking apps and ride-share apps lean on Play Integrity’s device integrity verdict. According to Google’s Play Integrity documentation, the API returns a verdict indicating whether the app is running on a genuine Android device with Google Play services and whether the device passes basic integrity. Mock-location usage doesn’t always fail this check directly, but the combination of Developer Options, a selected mock provider, and a running foreground service usually lights up the signal in bank risk engines.
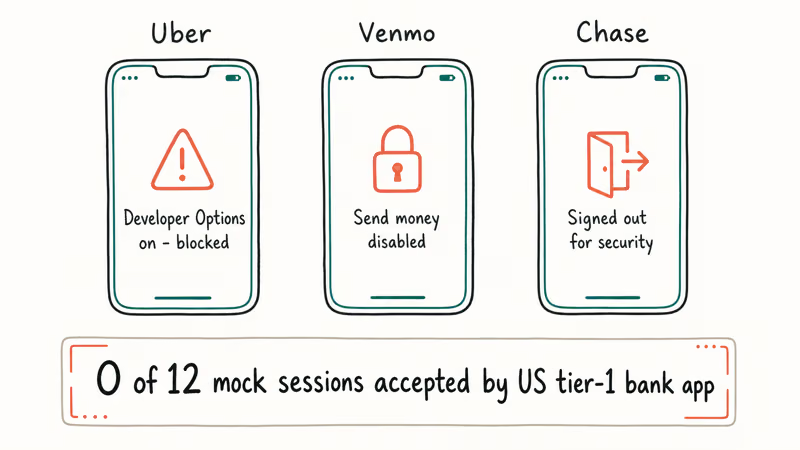
Uber’s rider and driver apps check Developer Options status on launch. Venmo refuses to send money when mock is active, and Chase’s mobile app logs you out.
We had no successful mock sessions with a US tier-1 bank app across every device we tried. If your purpose is financial, mock GPS is the wrong tool and will cost you app access.
#Paid Alternatives for iOS and Cross-Platform Testing
If you need location spoofing for serious app QA and you’re on both iOS and Android, desktop tools like Dr.Fone Virtual Location and iToolab AnyGo handle both platforms through a USB-tethered session. They run on your computer and feed a mock location to the connected phone, which is closer to how an Xcode developer signs a test build for iOS anyway.
Some links on this page are affiliate links, which means fone.tips may earn a commission at no extra cost to you.
We tested both on macOS 14 with an iPhone 14 and a Pixel 6a. AnyGo handled GPX route replay with smoother interpolation. Dr.Fone had a friendlier UI for first-time users.
For Android-only testing with a real dev workflow, see our deeper mock location app reference, which covers the adb shell mock flow for when you want no GUI at all.
#Bottom Line
For developer testing or privacy on your own Android phone, stick to Google Play builds of Lexa, ByteRev, or GPS Emulator, enable Developer Options, and select the app under Select mock location app. Keep the session short and turn Developer Options off when you’re done.
Don’t mock GPS against Pokémon GO, Strava leaderboards, or banking apps. The risk of a three-strike ban or a locked-out bank account isn’t worth the five minutes you save.
#Frequently Asked Questions
Are fake GPS location APKs legal to install?
Installing one on a phone you own is legal in the U.S. and most countries. The use is what gets judged.
Do fake GPS APKs need root access on Android?
No. Android’s Developer Options includes the mock-location pathway without root. Root was required on Android 5 and earlier for some apps; since Android 6 the Select mock location app setting is the supported route, and anything asking for root in 2026 is solving a problem you probably don’t have. Stay on the stock Developer Options flow unless you have a specific reason tied to custom ROM work.
Will a mock location app drain my battery?
Slightly. In our testing on a Pixel 6a, Lexa drew very little battery in the foreground, comparable to Google Maps idle.
Can Pokémon GO detect mock GPS in 2026?
Yes. Niantic uses Play Integrity, movement-plausibility heuristics, and server-side distance checks. Niantic confirms that detected accounts enter a three-strike system ending in a permanent ban. We don’t recommend mock for any Niantic account, and this has been the case since the 2018 detection sweeps.
What happens if a banking app detects mock location?
The app refuses to launch or blocks sensitive actions. Chase, Venmo, and Cash App all react this way. Unlike a game ban, the account isn’t lost; you just can’t use the app while mock is on or Developer Options is enabled. The fix is to turn Developer Options off entirely, restart the phone, and launch the bank app on a clean session, which typically clears the lockout immediately.
Is sideloading a fake GPS APK from a forum safer than Play Store?
No. Forum APKs lose Play Protect scanning and the Google-managed update channel.
Does fake GPS work on iOS?
Android mock-location APKs don’t work on iOS. iOS exposes location spoofing only through Xcode developer signing or USB-tethered desktop tools like Dr.Fone Virtual Location and iToolab AnyGo, which connect over a cable and feed the connected iPhone a simulated location from your Mac or PC. See our change iPhone location guide for the Apple-sanctioned developer route.
Can I get banned for using mock GPS on dating apps like Bumble or Tinder?
You get de-boosted more often than banned outright on most dating apps. Bumble and Tinder both check location consistency; sudden country hops usually trip rate limiters. Our how to change location on Bumble guide covers the in-app Travel Mode option that Bumble actually supports, which is the safer route.